The Unified Data
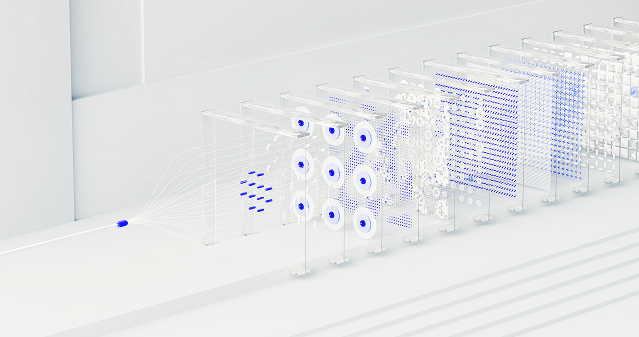
Trust Control Plane
A patented Zero Trust platform delivering the cryptographic trust layer for the age of Enterprise AI
Contact Us to Learn MoreBuilt By People from




The Core Challenge Is Data, Not Models
Fundamental constraint: enterprise data readiness. Despite high investment levels, most organizations are failing to scale AI:
~80% have experimented with AI agents | Only ~10–15% have achieved production deployment
Solving the Impediment to Enterprise AI Scalability
It's a Data Problem. Not a model problem.
Fragmentation Problem
Data spread across disconnected systems. Enterprise data is spread across warehouses, lakes, object stores, catalogs, BI tools, identity systems, and AI applications, while access policies are often implemented separately in each environment. This leads to inconsistent enforcement, limited visibility, and difficulty proving who has access to what.
Structure Problem
~90% of enterprise data is not AI-ready. Valuable enterprise information increasingly resides in files, documents, object storage, and other non-tabular formats rather than only in structured databases. This matters because AI and RAG workflows ingest both structured and unstructured data, often at high speed and scale.
Trust Problem
Data cannot reliably support automated decision-making. Companies lack sufficient confidence in whether data is safe, appropriate, and authorized for a given use case. Data becomes untrusted when organizations lack accurate metadata, classification, access context, policy enforcement, and auditability.
Enterprise Data is Everywhere. You Need a Way to Capture & Control it.
Fragmented Enterprise Systems
Critical knowledge is scattered across SaaS platforms, data warehouses, shared drives, internal applications, tickets, chats, logs, and legacy infrastructure.
Unstructured Data at Scale
Most enterprise knowledge was built for humans, not AI — requiring interpretation, structuring, and governance before it can be reliably operationalized.
Inconsistent Trust & Authority
AI cannot reliably make decisions without knowing which sources are authoritative, who owns the data, whether it is current, or what permissions apply.
Risky Access Control
Granting broad access introduces security and compliance risks, while overly restrictive controls limit usefulness — requiring granular, policy-aware governance.
DC2 - Data Command and Control
Primary.AI's DC2 control plane sites as the governing layer between AI agents and the enterprise systems they can access, covering connection, identity, runtime policy enforcement, security inspection, and observability across prompts, responses, and tool calls.
Move from AI pilots to production AI
The Power of our ABAC Unified Policy Engine
Regain Control
Reduce risk from uncontrolled data access. Data teams can centrally define access policies and enforce them consistently. Instead of managing permissions platform by platform, organizations can use a unified control plane to automate provisioning, simplify policy management, and deliver governed access at scale.
Zero Trust Access
Enable agents to act within approved boundaries. AI and analytics are only as reliable as the data behind them. With Primary.AI you no longer question which data is sensitive, who should be allowed to use it, whether policies are current, and whether access decisions are being applied consistently.
Visibility
Maintain visibility across AI, data, and workflow activity. Through logging, classification, access monitoring, and audit capabilities, Primary.AI helps organizations understand activity across their data environment. Dynamic access policies allow admins to customize the granularity of monitoring activity for security, compliance and data privacy considerations.
AI-ready data is not just connected. It is trusted.
Secure your workforce without compromising speed. One browser for compliance, threat prevention, and total data control.
Zero Trust
True Zero Trust for clear sources of truth, owners, and confidence signals. Continuous authorization and full workflow visibility enforces risk-based permissioning to users and agents.
Compliance
Data Access is controlled by identity, role, policy, workflow context, and business rules.
Insider & Outsider Threats
Traceable from input to output, with visibility into what data was used and why.
Dynamic Intelligence
Context Aware to support decisions, recommendations, and automated action.
Federated
Federated Policy Enforcement enable real-time controls at machine-speed.
Quantify your Security, AI Spend, and Utilization Productivity
Telemetry-Driven Decisions
Turn operational telemetry into clear, actionable business decisions.
Security & AI ROI Visibility
Measure the true ROI of your security, data, and AI investments.
Workflow Intelligence
Analyze how data moves through workflows to optimize control, access, and utilization
Redefine Data Control for Agents
Your Data, Your Rules.
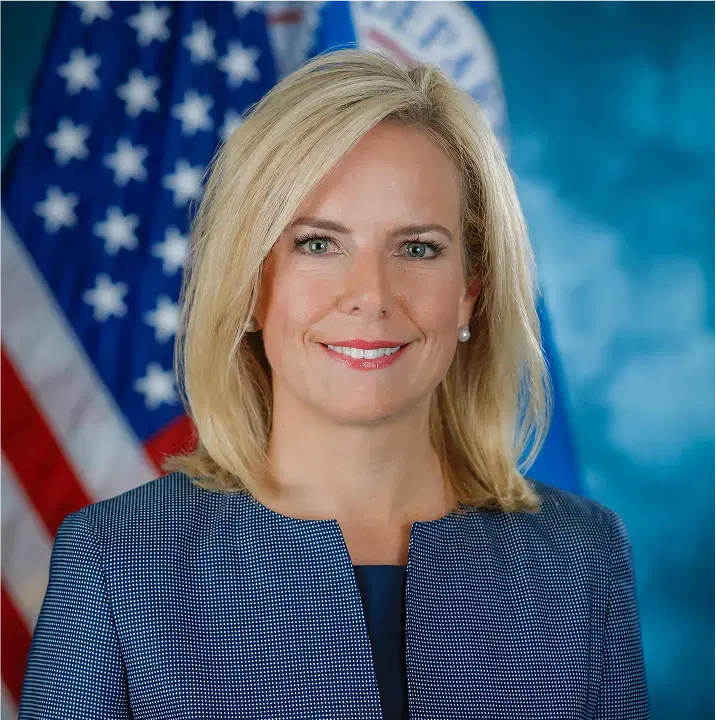
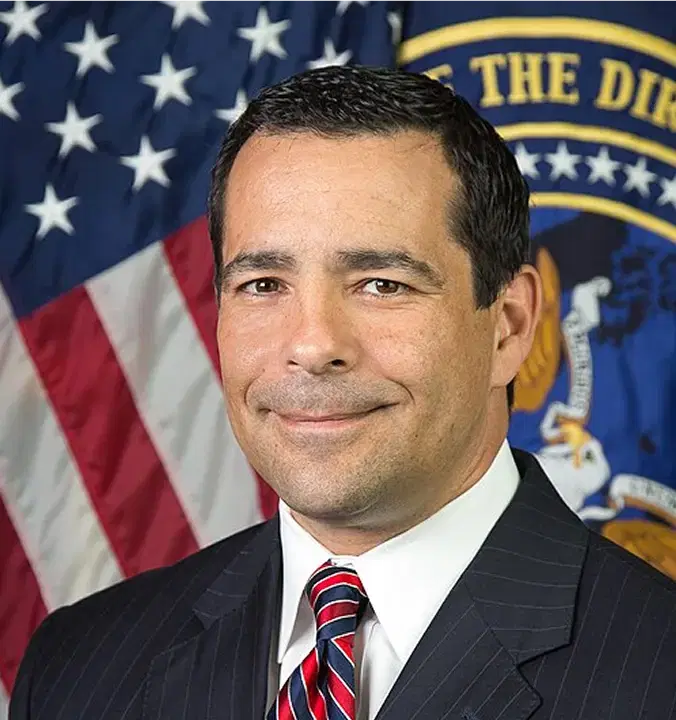
Executive Team includes former leadership of




Validated by those with Operating Experience From
Own the Control Layer for AI
Remove the last impediment to scalable AI ROI
Primary.AI is trusted and actively used by some of the largest Fortune 100 Companies in the world.